QR code-based attacks
Scam related campaigns
Business email compromise
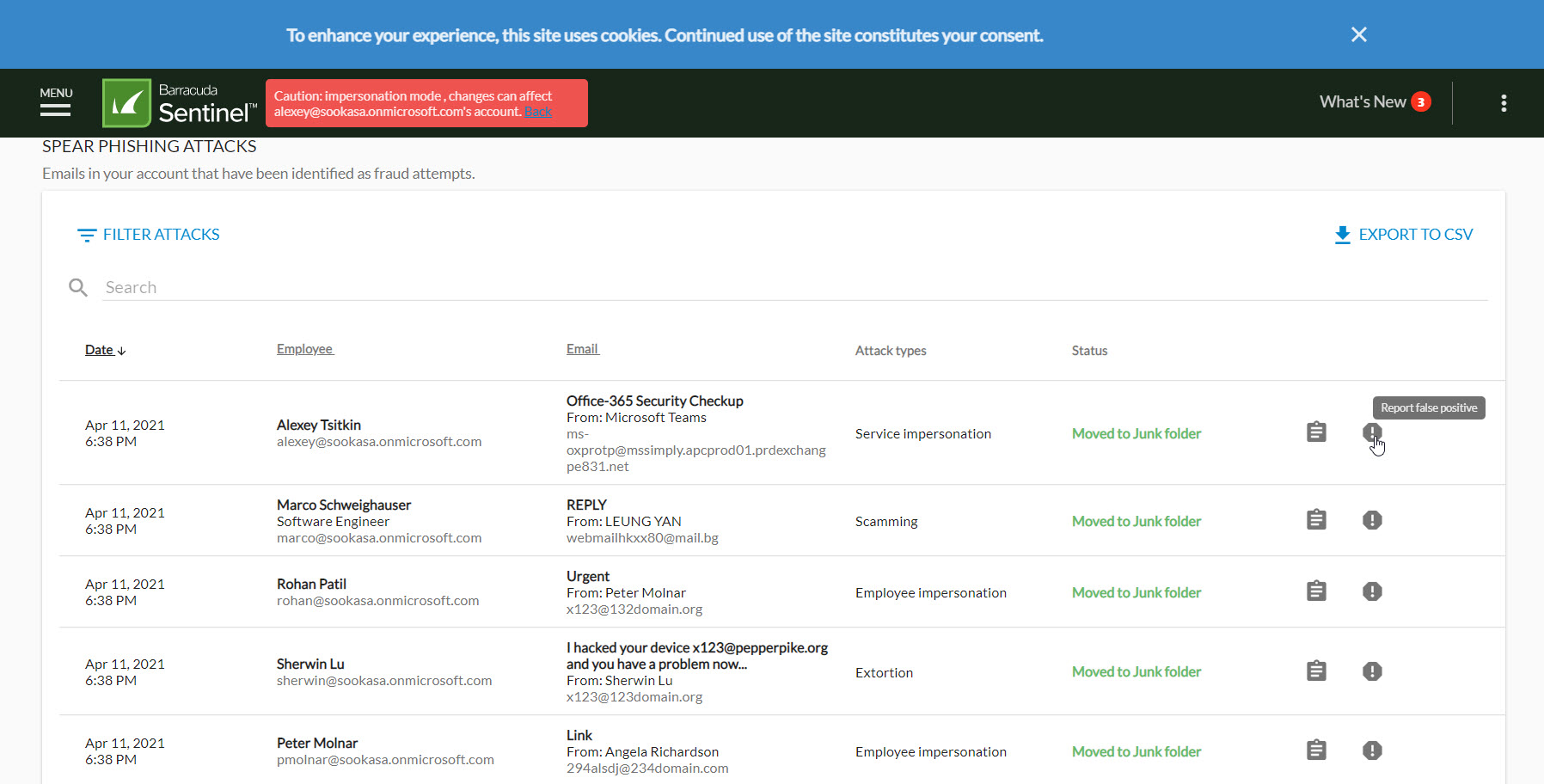
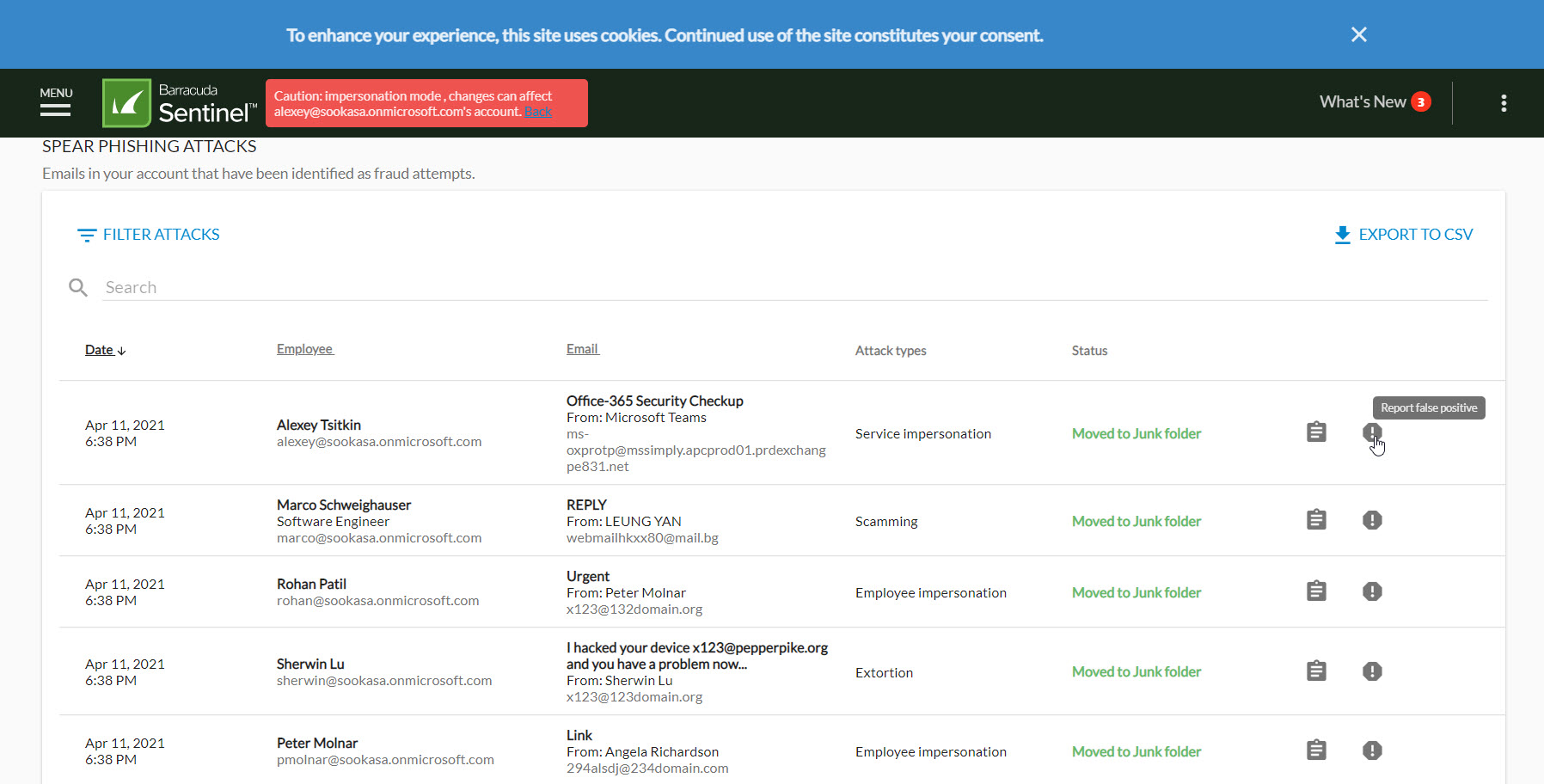
Admin users will see these detections on the Impersonation Protection UI. We encourage all users to submit missed emails and incorrect detections via the Barracuda Email Protection Add-In.
]]>QR code-based attacks
Scam related campaigns
Business email compromise
Admin users will see these detections on the Impersonation Protection UI. We encourage all users to submit missed emails and incorrect detections via the Barracuda Email Protection Add-In.
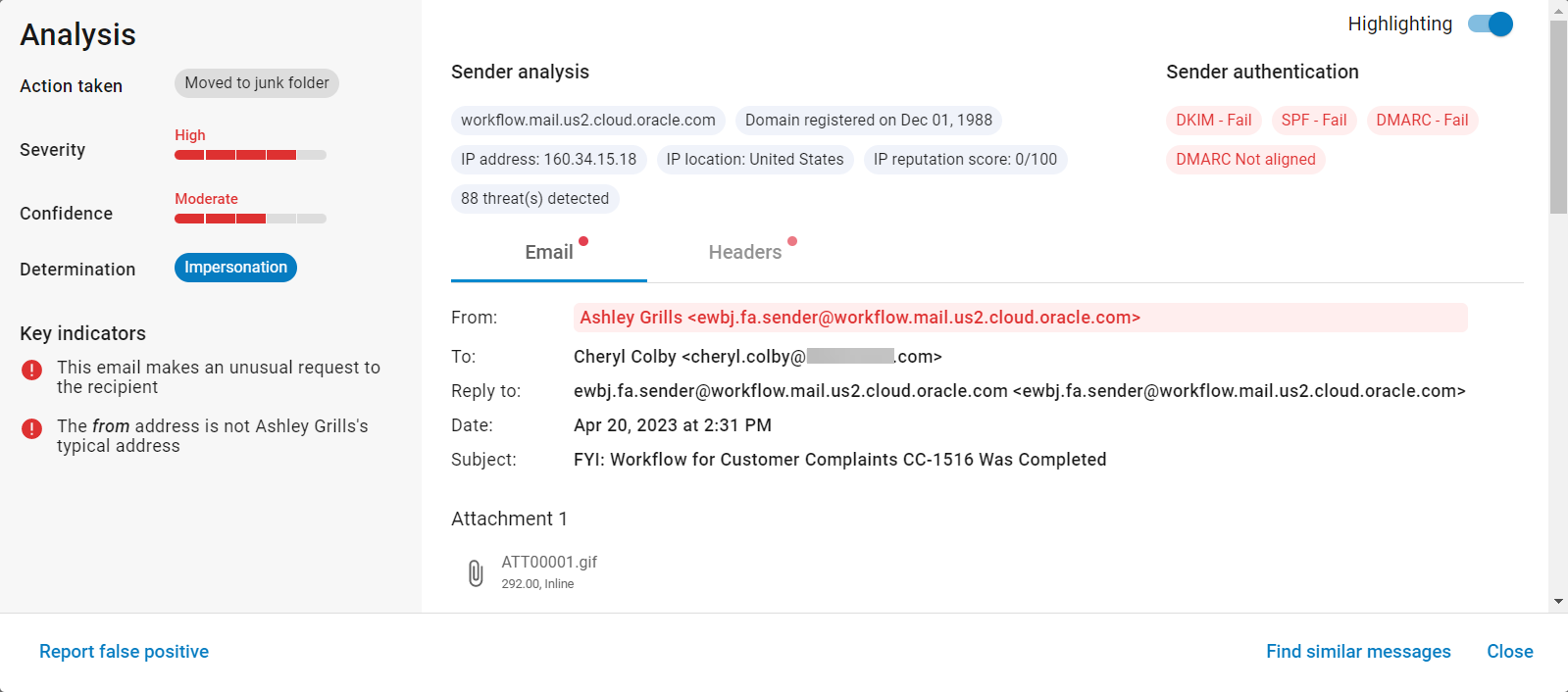
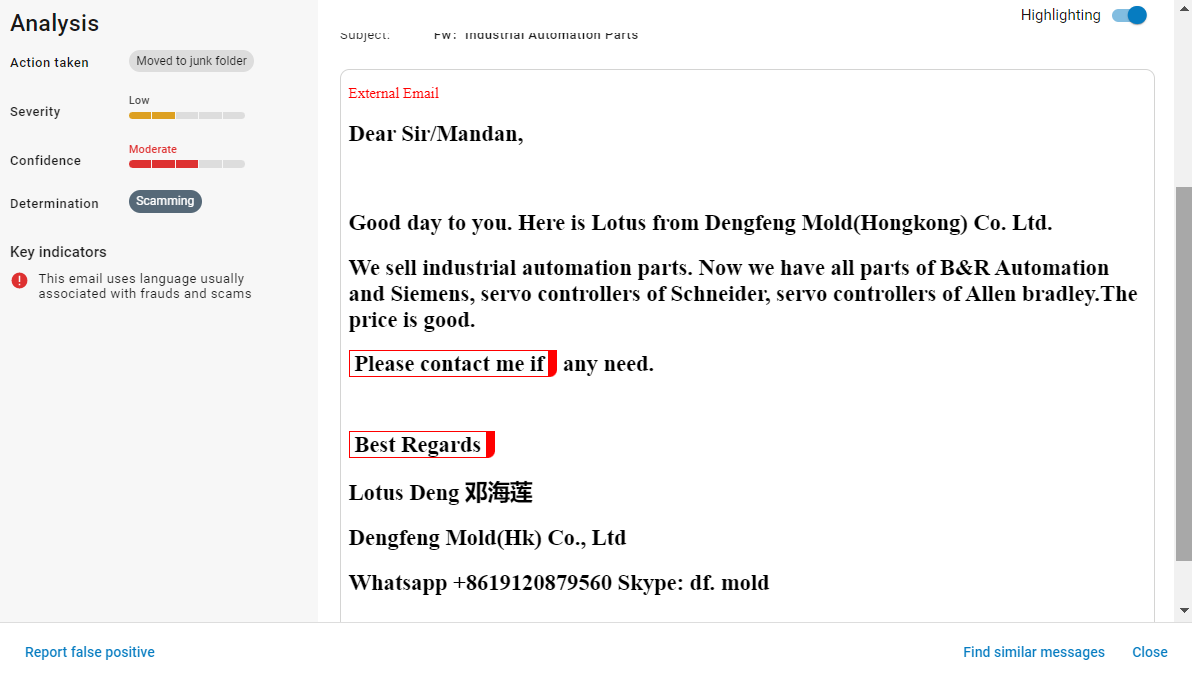
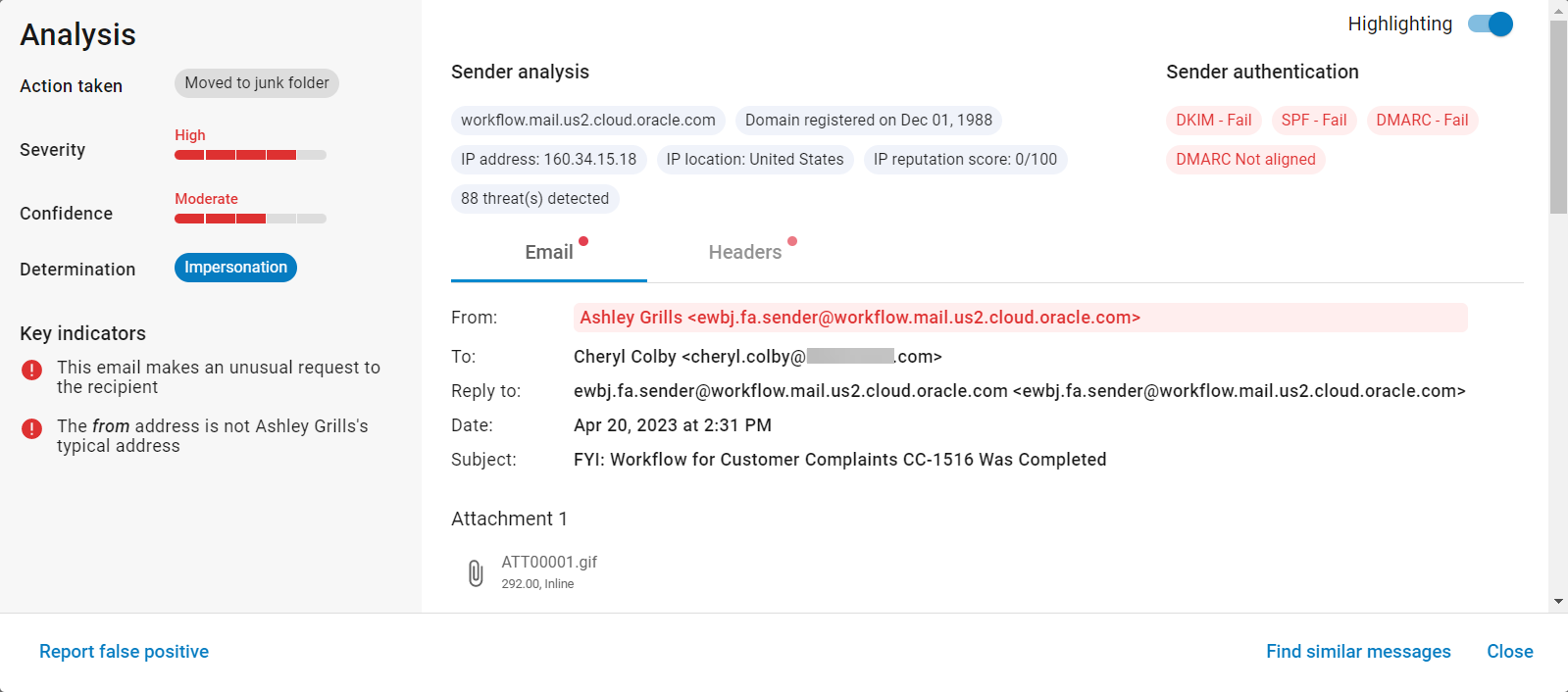
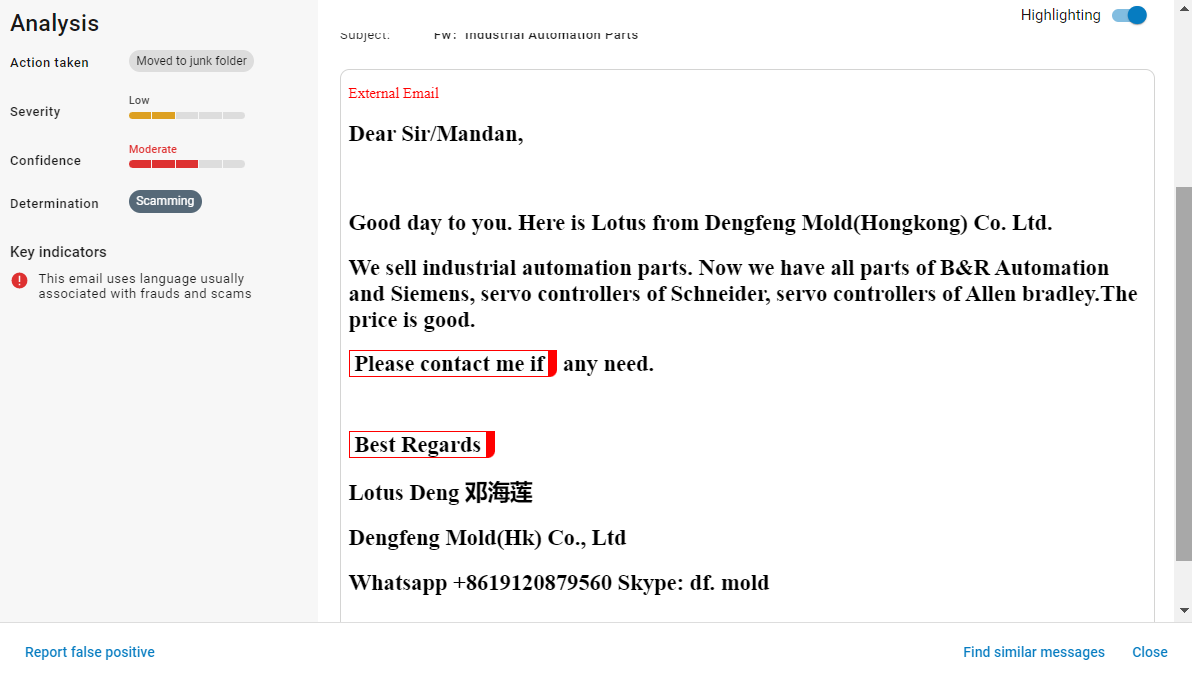
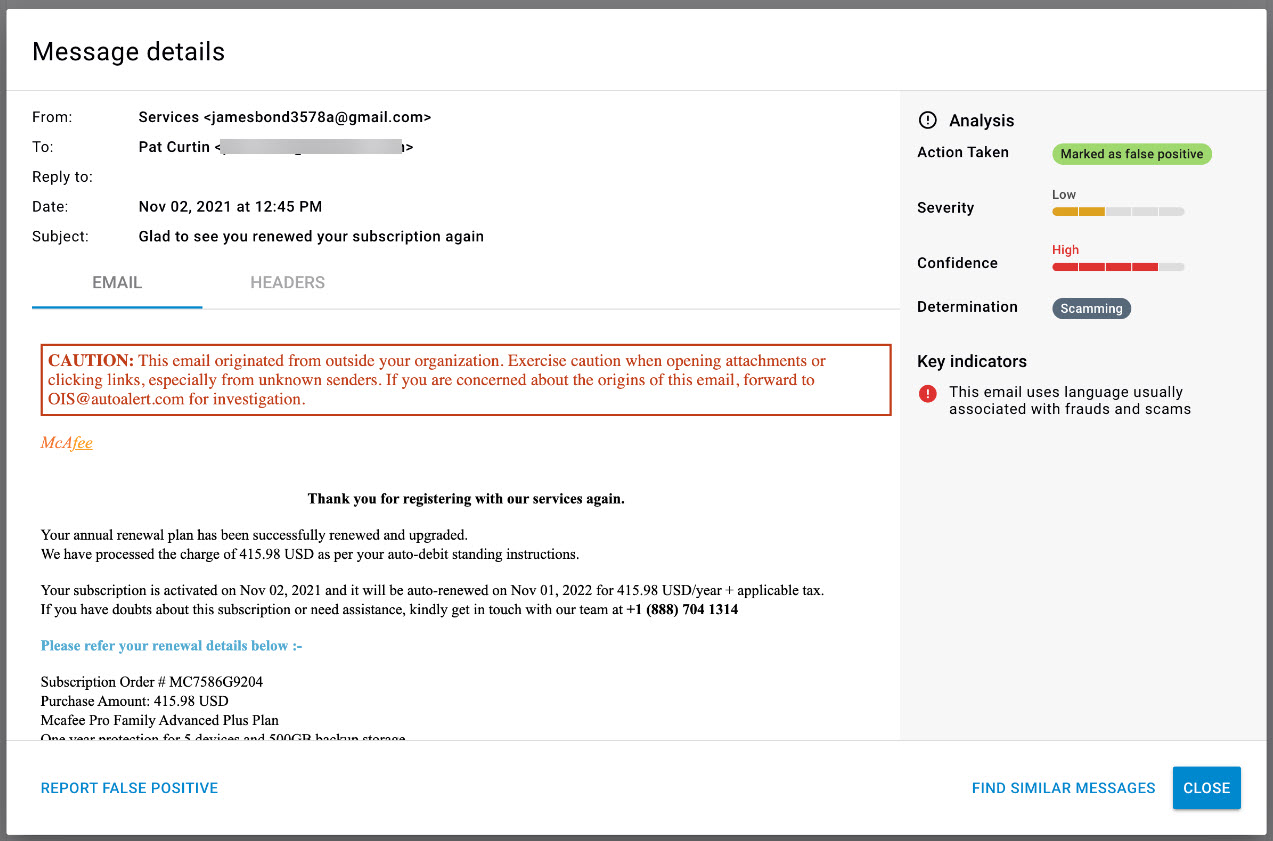
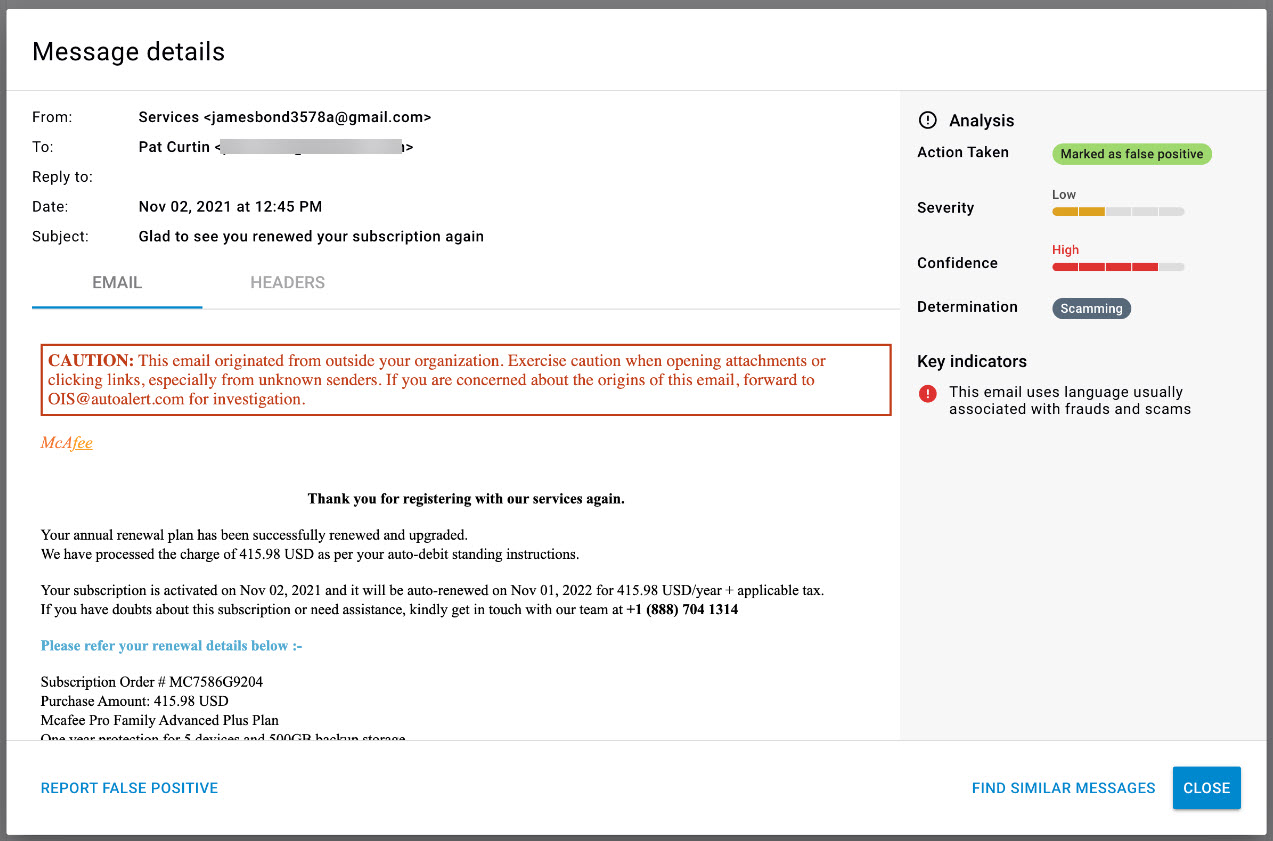
]]>To Enable Highlighting:
From within a message, toggle to enable Highlighting at top-right to see the elements of a message that Barracuda Impersonation Protection deem as suspicious. Keywords and phrases in the message content will have red boxes around them. Other identifiers, shown via the Sender Information chips and Header information will display in red. The Email and Header tabs will show red dots if they display suspicious information.
Learn more on campus
]]>To Enable Highlighting:
From within a message, toggle to enable Highlighting at top-right to see the elements of a message that Barracuda Impersonation Protection deem as suspicious. Keywords and phrases in the message content will have red boxes around them. Other identifiers, shown via the Sender Information chips and Header information will display in red. The Email and Header tabs will show red dots if they display suspicious information.
Learn more on campus
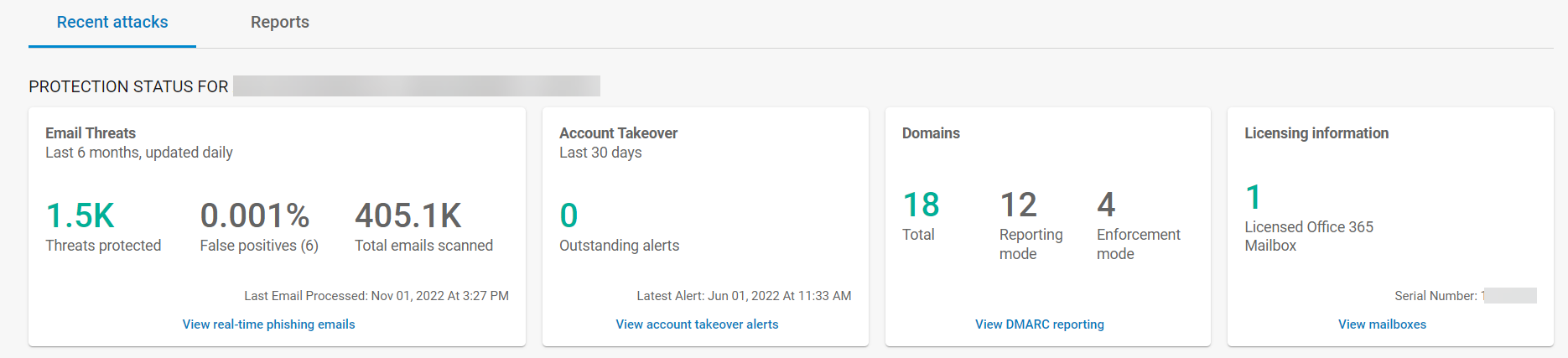
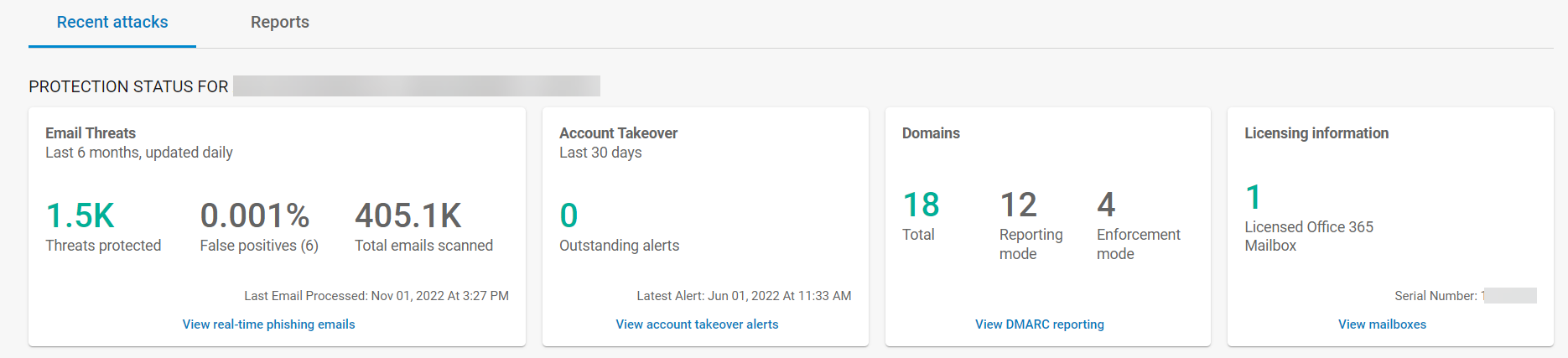
]]>False positives is the percentage of messages marked as threats that were actually good emails. An asterisks here means the percentage is less than 0.001%. You can hover over this number to see the actual percentage.
Campus: https://campus.barracuda.com/product/sentinel/article/preview/98212871
]]>False positives is the percentage of messages marked as threats that were actually good emails. An asterisks here means the percentage is less than 0.001%. You can hover over this number to see the actual percentage.
Campus: https://campus.barracuda.com/product/sentinel/article/preview/98212871
]]>Over the last couple of months, we have worked to improve our efficacy by improving detections and reducing false positives. Here are a few examples:
Introduced a new classifier that identifies emails containing bad URLs from services utilizing IPFS links, which increased phishing detections.
HTML has now replaced PDF as the most weaponized artifact. We have added improvements to HTML attachment classifier as well as HTML classifier to further improve phishing detections.
ATO classifier enhancements to include impossible travel and other features to improve ATO detections and reduce false positives.
While most of our classifiers are language independent, there are some classifiers that perform better when trained in different languages. Our CEO Fraud classifier is one such classifier which has been enhanced through native Spanish, German, Italian, French, Portuguese, and Dutch support. In addition, Simple CEO classifier and BAIT (reconnaissance) classifiers have also been added to improve BEC detections.
A new classifier has been added to detect fake invoices which are embedded in emails.
Phish masking is a common technique used by attackers to hide malicious URLs behind link forwarding or shortening services. Many attackers use multiple forwarders (bit.ly, goo.gl or tiny URL for example) to evade detection. For example, a phishing_link.com maybe wrapped x number of times before the malicious link is finally opened. Attackers are also known to utilize well known services like Salesforce and SendGrid (just to name a couple) to mask their URLs. Ability to dynamically resolve and expand URLs has been greatly enhanced.
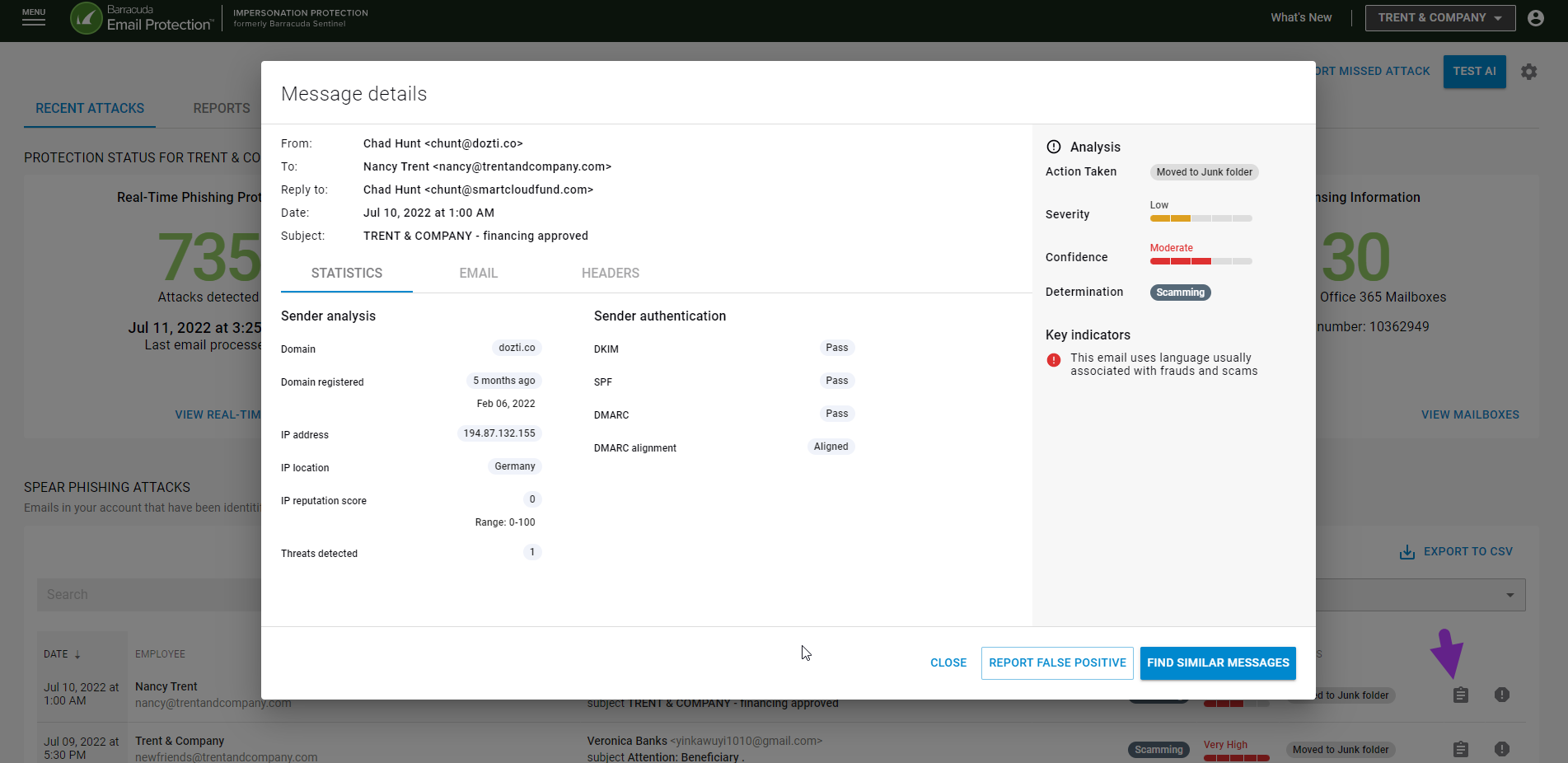
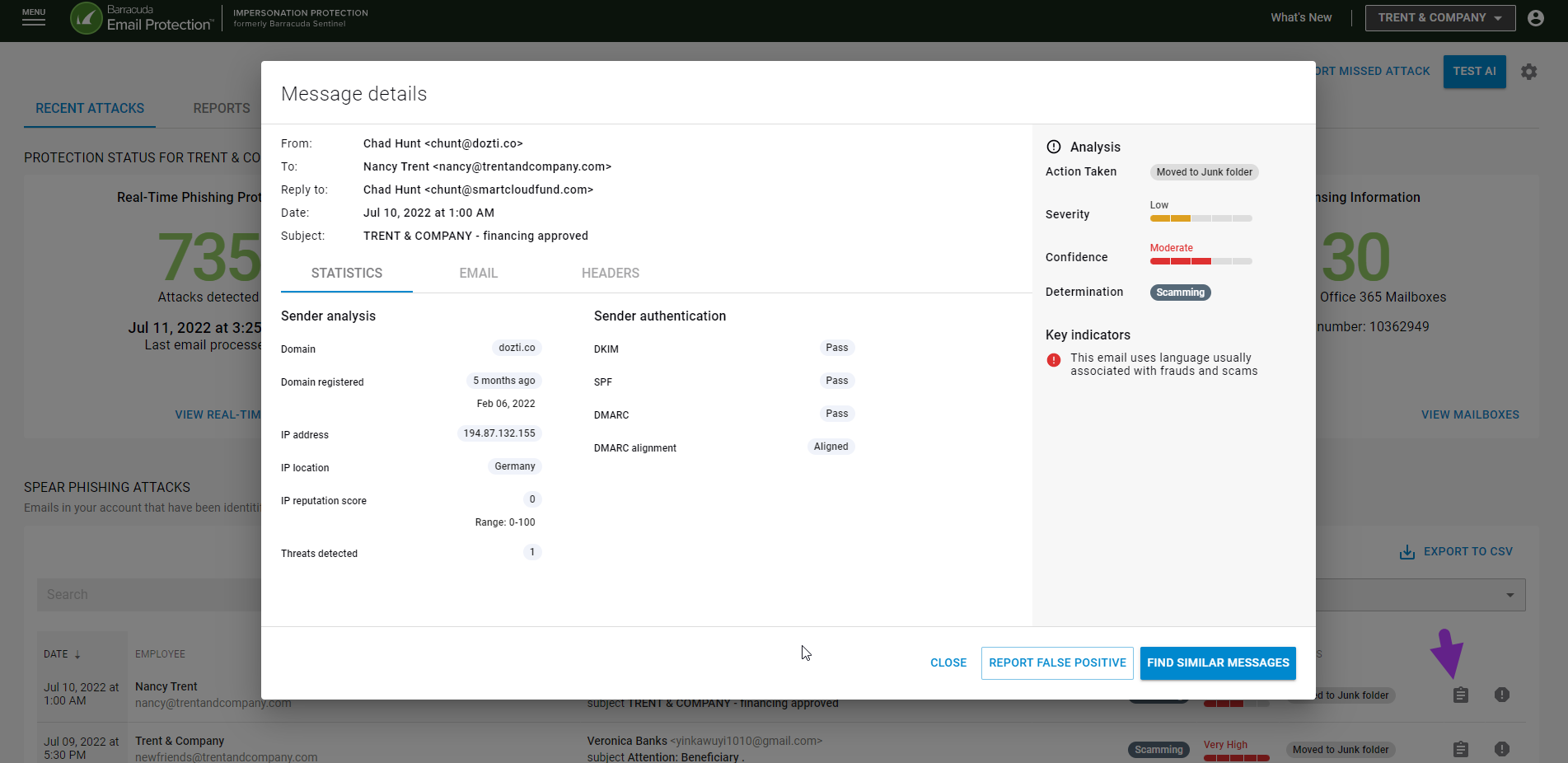
UI Enhancements:
In addition to the improvements to our classifiers we are pleased to announce that our migration efforts to the new, more engaging technology is now complete. This allows us to quickly build and iterate on new features that you have asked for. One such feature is the addition of the “Statistics Tab”. To help you better understand why an email was blocked, we now have Sender Analysis and Sender Authentication details in addition to Confidence & Severity level, and Key Indicators when you click on more details to review an alert.
Over the last couple of months, we have worked to improve our efficacy by improving detections and reducing false positives. Here are a few examples:
Introduced a new classifier that identifies emails containing bad URLs from services utilizing IPFS links, which increased phishing detections.
HTML has now replaced PDF as the most weaponized artifact. We have added improvements to HTML attachment classifier as well as HTML classifier to further improve phishing detections.
ATO classifier enhancements to include impossible travel and other features to improve ATO detections and reduce false positives.
While most of our classifiers are language independent, there are some classifiers that perform better when trained in different languages. Our CEO Fraud classifier is one such classifier which has been enhanced through native Spanish, German, Italian, French, Portuguese, and Dutch support. In addition, Simple CEO classifier and BAIT (reconnaissance) classifiers have also been added to improve BEC detections.
A new classifier has been added to detect fake invoices which are embedded in emails.
Phish masking is a common technique used by attackers to hide malicious URLs behind link forwarding or shortening services. Many attackers use multiple forwarders (bit.ly, goo.gl or tiny URL for example) to evade detection. For example, a phishing_link.com maybe wrapped x number of times before the malicious link is finally opened. Attackers are also known to utilize well known services like Salesforce and SendGrid (just to name a couple) to mask their URLs. Ability to dynamically resolve and expand URLs has been greatly enhanced.
UI Enhancements:
In addition to the improvements to our classifiers we are pleased to announce that our migration efforts to the new, more engaging technology is now complete. This allows us to quickly build and iterate on new features that you have asked for. One such feature is the addition of the “Statistics Tab”. To help you better understand why an email was blocked, we now have Sender Analysis and Sender Authentication details in addition to Confidence & Severity level, and Key Indicators when you click on more details to review an alert.
As part of our efforts to faster development and moving to newer technology, your UI now has a new look when you log into Impersonation Protection. Here is the new look:
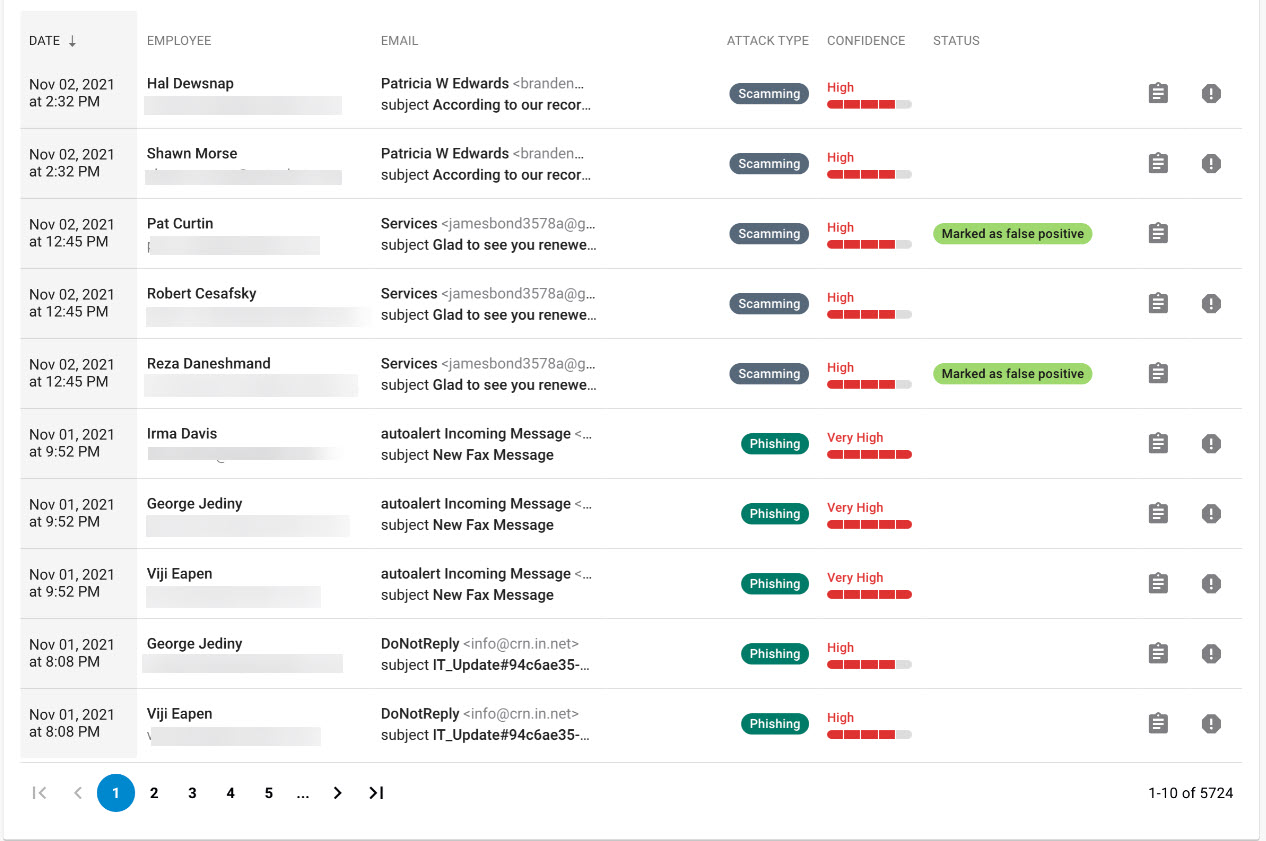
Benefits to you
Our users are always at the heart of our innovations and this release gives us greater flexibility and increased speed in integrating the new features you have been requesting
You now have visibility into the confidence score each email gets when processed via Impersonation Protection
You can also see the severity of a threat against each email
You have the ability to set up different email addresses for ATO alerts vs Phishing alerts.
As part of our efforts to faster development and moving to newer technology, your UI now has a new look when you log into Impersonation Protection. Here is the new look:
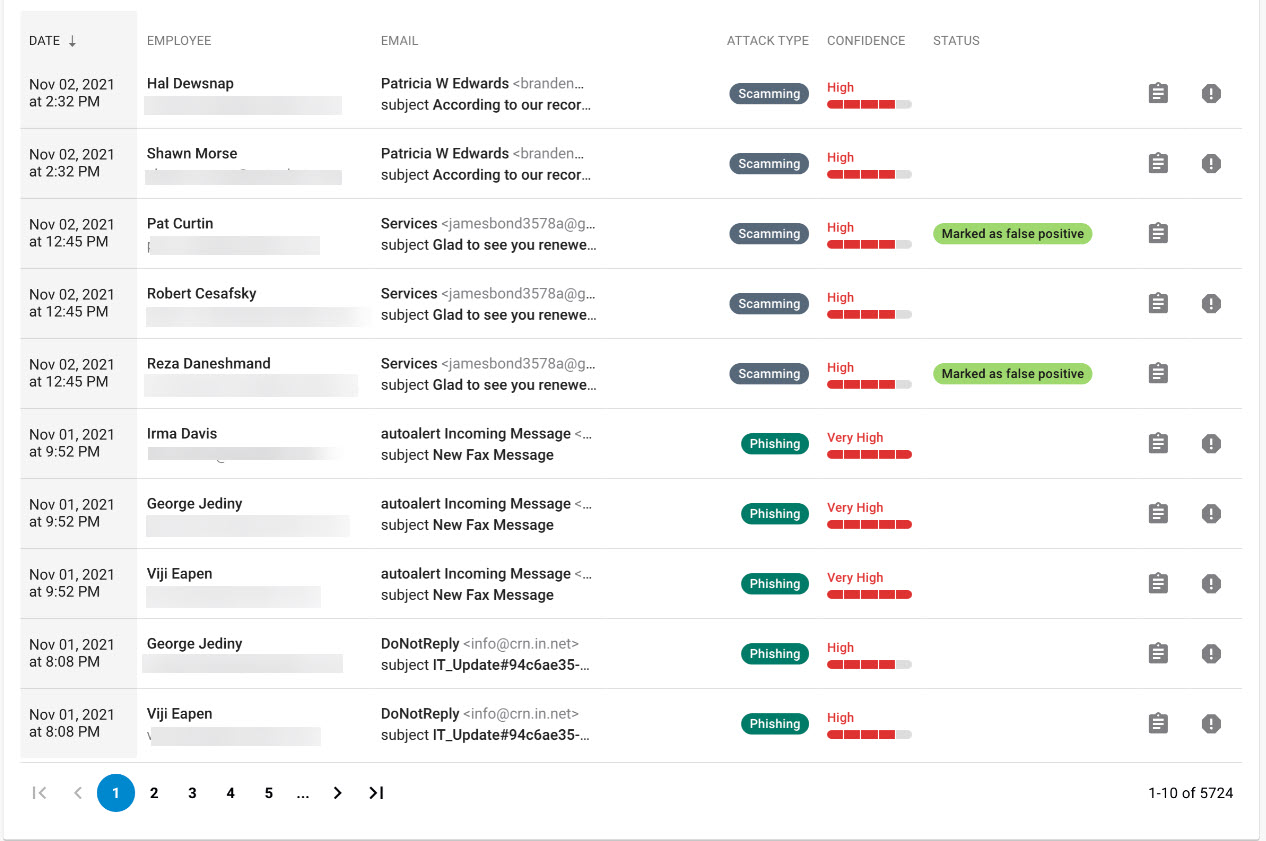
Benefits to you
Our users are always at the heart of our innovations and this release gives us greater flexibility and increased speed in integrating the new features you have been requesting
You now have visibility into the confidence score each email gets when processed via Impersonation Protection
You can also see the severity of a threat against each email
You have the ability to set up different email addresses for ATO alerts vs Phishing alerts.
]]>
]]>
To schedule email reports:
Open Barracuda Sentinel.
Click the Settings icon to access the administrative functions.
Select the Reports tab.
By default, Send reports by email is set to On (blue).
Select the time range for the data you want to see in the reports. Options are Last 7 Days, Last 30 Days, or Last 90 Days. The default value is Last 30 Days.
Specify the report recipient. By default, emails are sent to the security team email specified on the Remediation tab.
To specify a different recipient, switch the toggle to Off (grey) and type one email address in the Send to field that appears.In the Start date field, type or select the date you want to start receiving automated emails.
In the Frequency field, specify how often you want to receive reports. Options are Daily, Weekly, and Monthly. The default value is Monthly.
Click Save.
Discontinuing Email Reports
If you do not want to receive these automated emails, you can stop them by changing the settings to toggle off for Send reports by email
In the future we plan to support other formats. However, for now an email will be sent with the data requested.
]]>To schedule email reports:
Open Barracuda Sentinel.
Click the Settings icon to access the administrative functions.
Select the Reports tab.
By default, Send reports by email is set to On (blue).
Select the time range for the data you want to see in the reports. Options are Last 7 Days, Last 30 Days, or Last 90 Days. The default value is Last 30 Days.
Specify the report recipient. By default, emails are sent to the security team email specified on the Remediation tab.
To specify a different recipient, switch the toggle to Off (grey) and type one email address in the Send to field that appears.In the Start date field, type or select the date you want to start receiving automated emails.
In the Frequency field, specify how often you want to receive reports. Options are Daily, Weekly, and Monthly. The default value is Monthly.
Click Save.
Discontinuing Email Reports
If you do not want to receive these automated emails, you can stop them by changing the settings to toggle off for Send reports by email
In the future we plan to support other formats. However, for now an email will be sent with the data requested.
]]>If you choose to provide these details, you will be redirected to a feedback response form to select a reason from a list of options or to type in a reason.
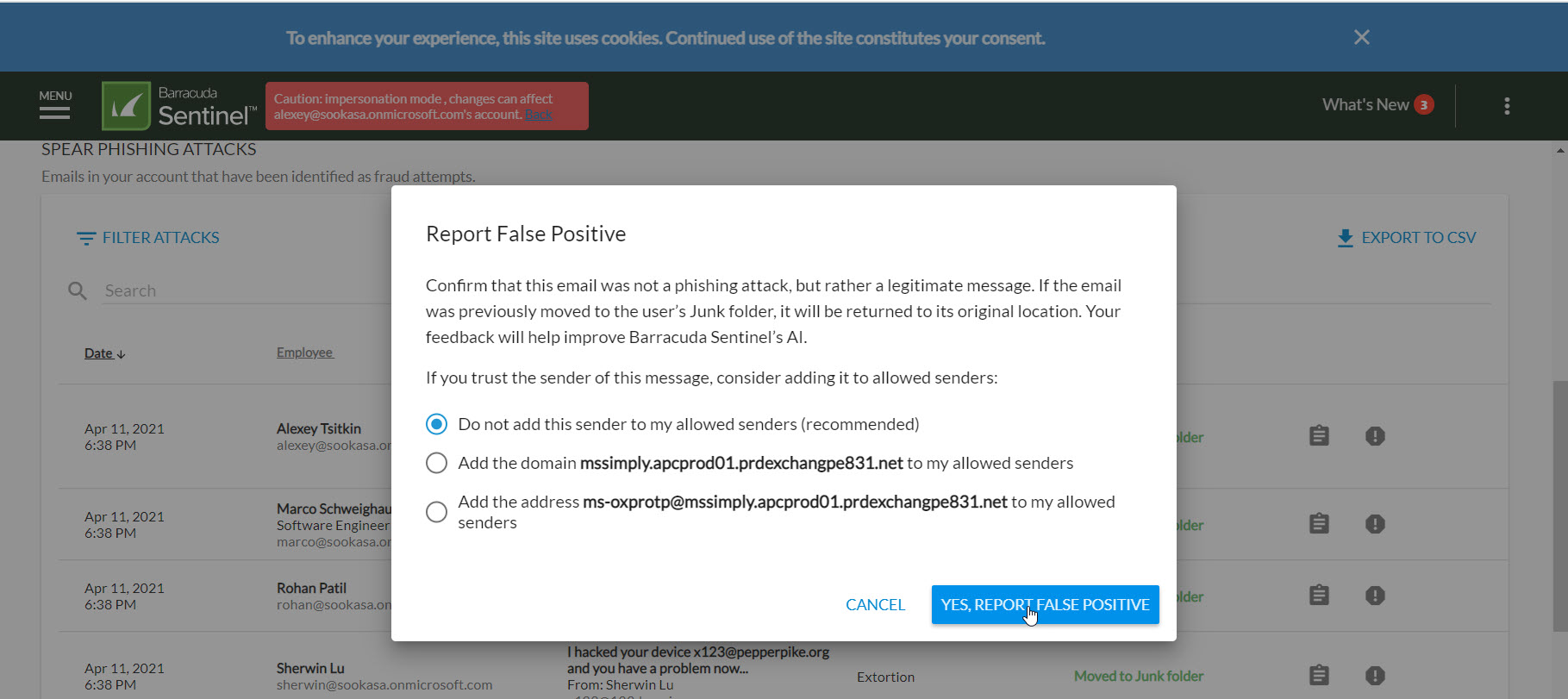
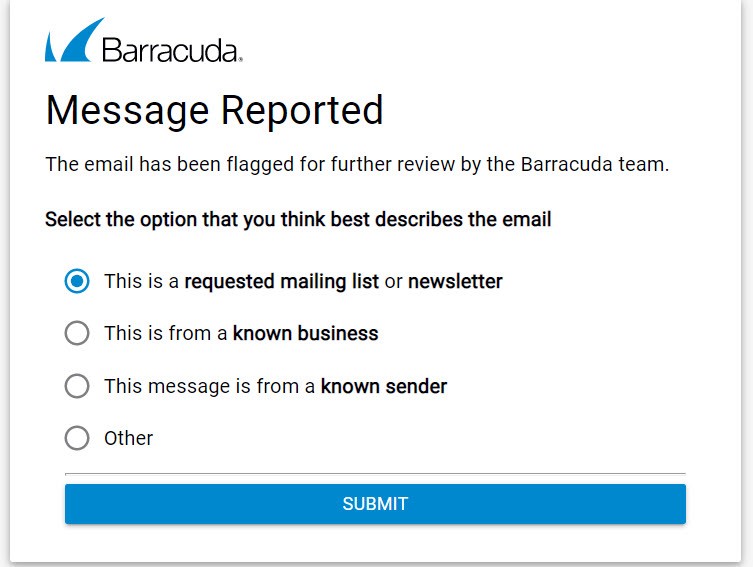
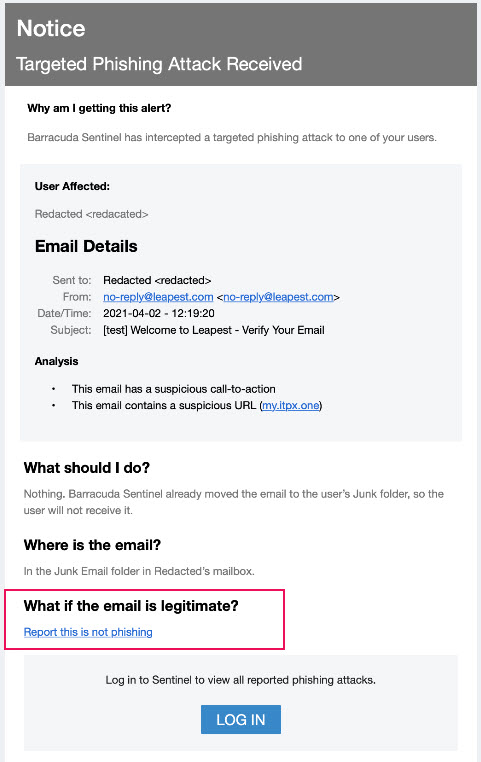
You can also find this information on campus here: https://campus.barracuda.com/product/sentinel/doc/80740499/false-positives/
]]>If you choose to provide these details, you will be redirected to a feedback response form to select a reason from a list of options or to type in a reason.
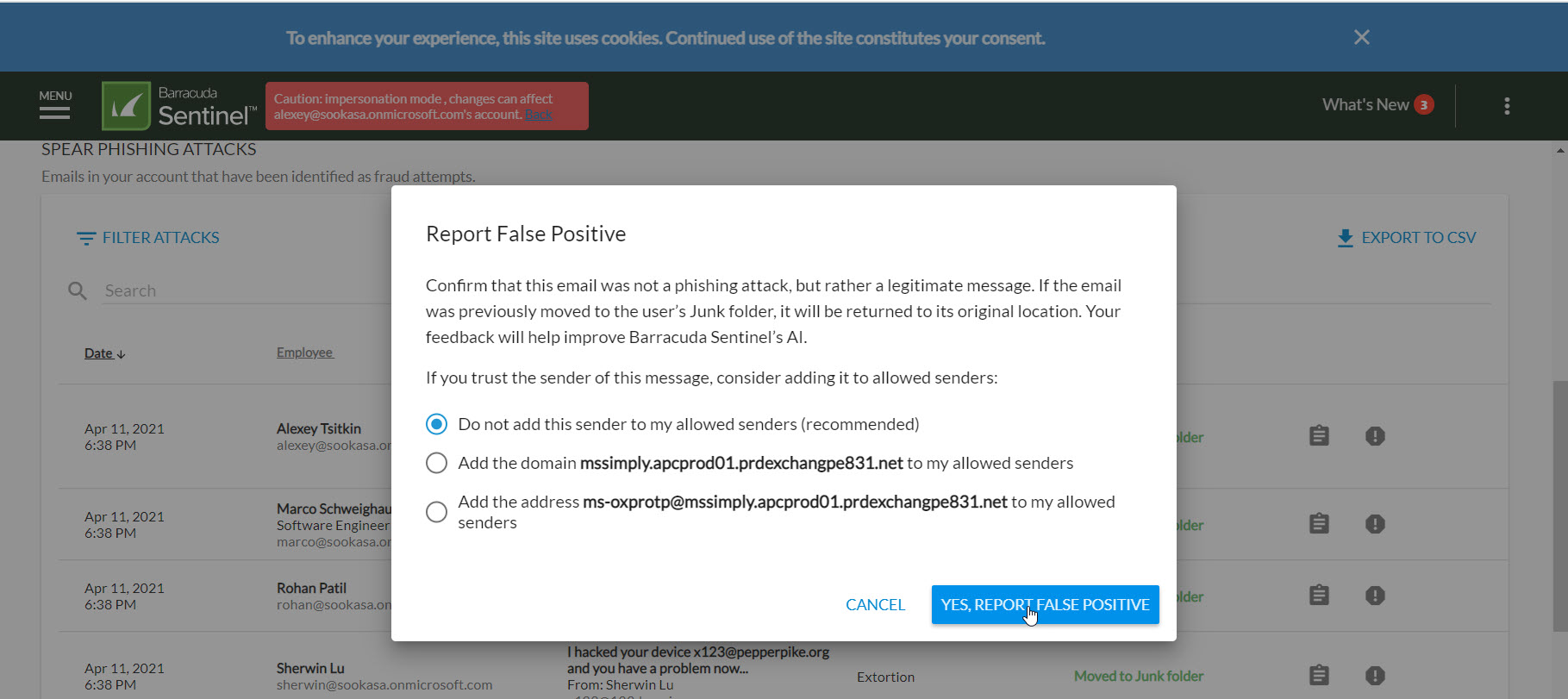
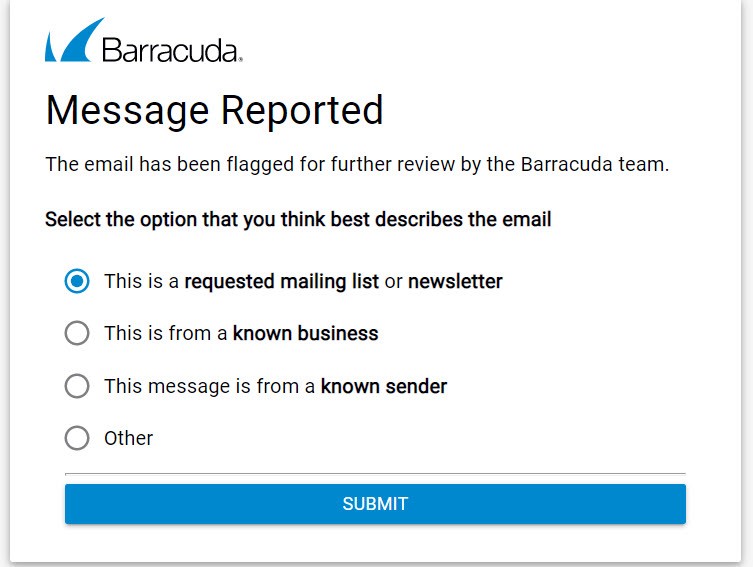
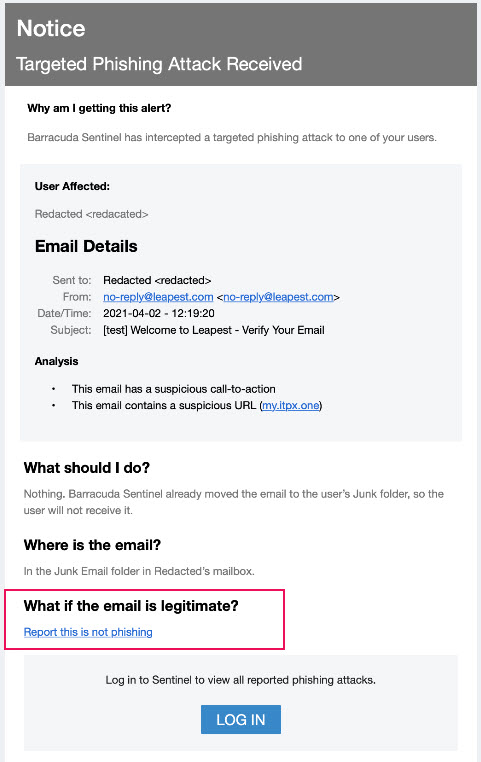
You can also find this information on campus here: https://campus.barracuda.com/product/sentinel/doc/80740499/false-positives/
]]>